Security Manual
Security Manual
# Overview
Zadig manages the entire software development lifecycle and supports almost all security tools and services on the market. For example, SAST tools like SonarQube(opens new window), Fortify(opens new window), and Coverity(opens new window), SCA tools like CleanSource(opens new window), and DAST tools like DongTai(opens new window). Zadig easily integrates these tools into the entire delivery pipeline, leveraging powerful runtime environment and workflow capabilities to provide strong support to security teams.
Zadig helps security teams shift security services and capabilities left to development, testing, and operations teams, enabling early identification of security issues and involving other roles in addressing security and compliance issues, avoiding additional costs from fixing such issues.
# Security Service Access
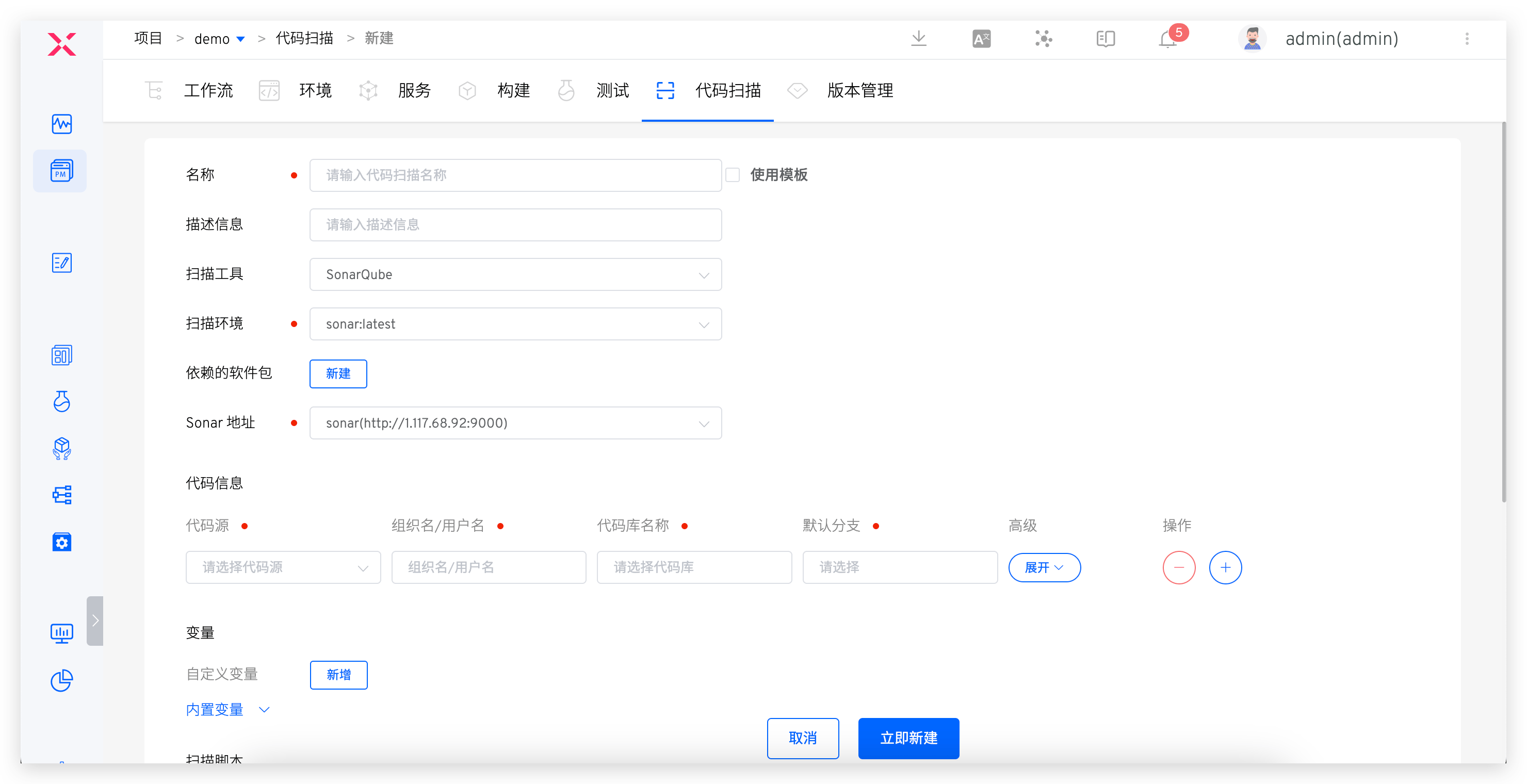
# Static Security SAST - Sonar
Step 1: Configure Code Scanning
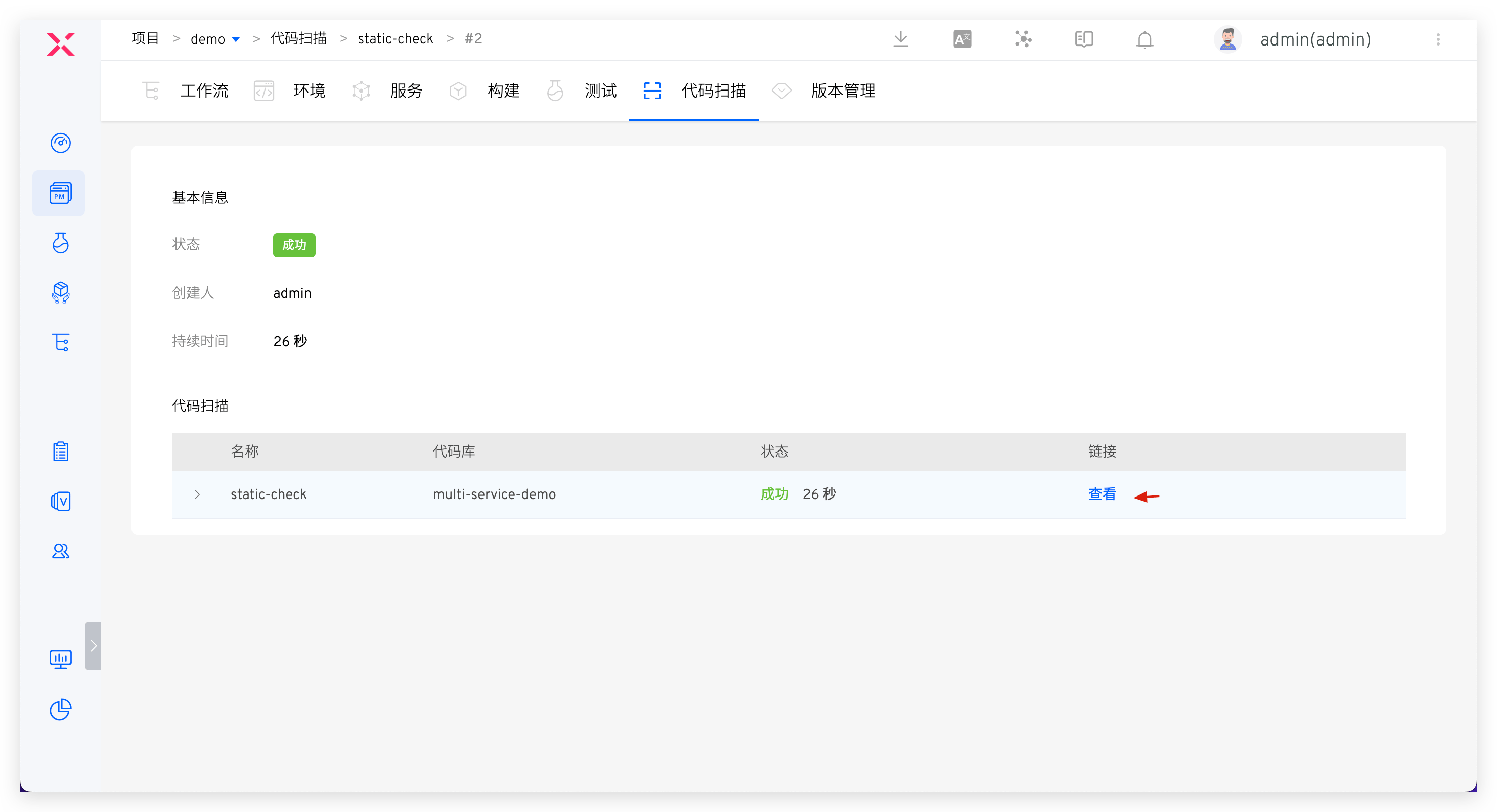
Add new code scan, select SonarQube scanning tool, and fill in code scanning configuration. See: Code Scanning.
Step 2: Orchestrate Code Scanning in Workflow
Edit workflow and add code scanning task at specified stage (e.g., before build task). See: Configure Workflow.
# Software Composition Analysis SCA - Fortify
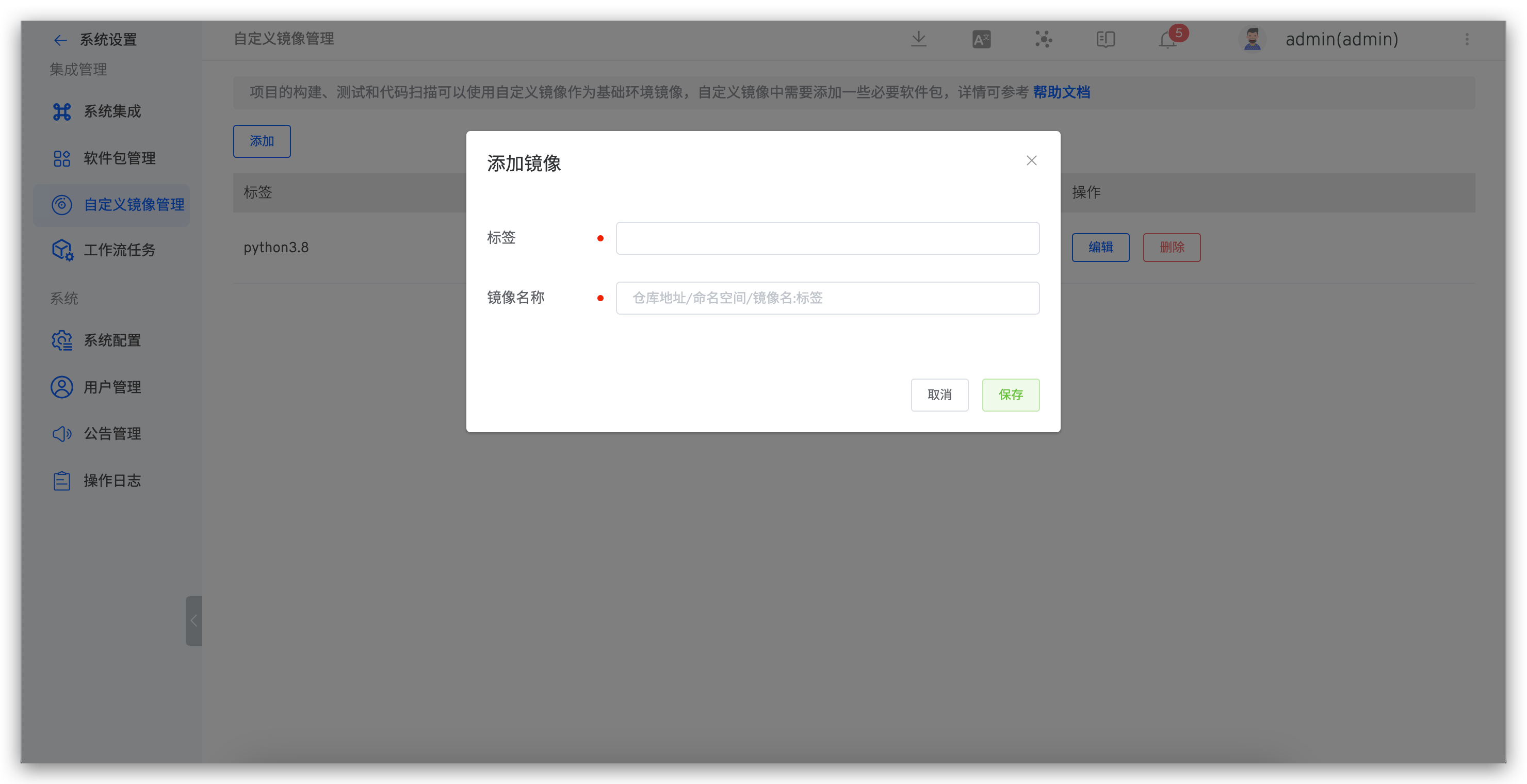
Step 1: Build Custom Image
- Build custom image and upload to image registry. See: Custom Image.
- Add custom image in Zadig. See: Add custom image.
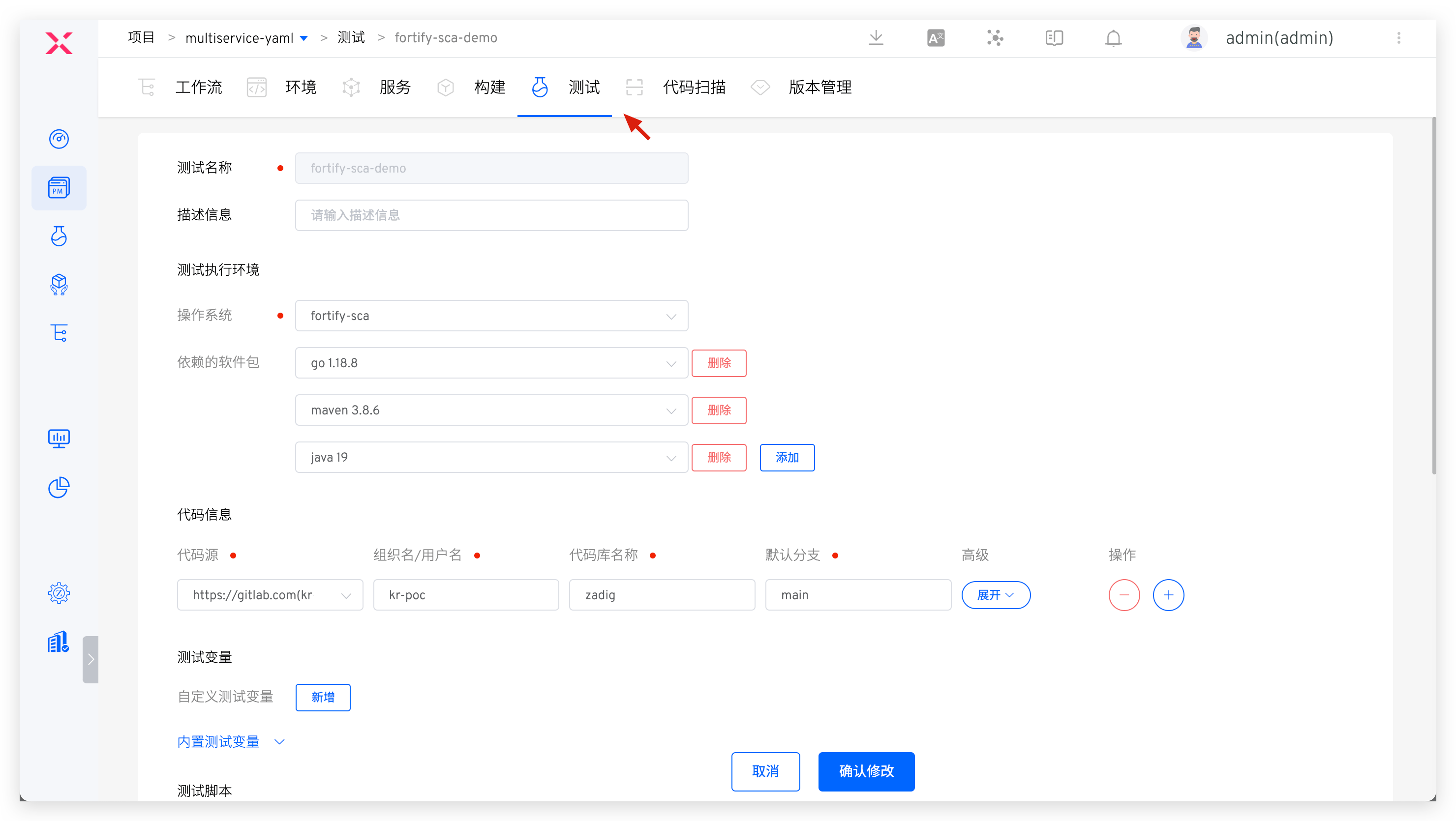
Step 2: Configure SCA Scan
Add new test and complete specific configuration for Fortify SCA code scanning. Relevant parameters explained below. For detailed information, see: Test.
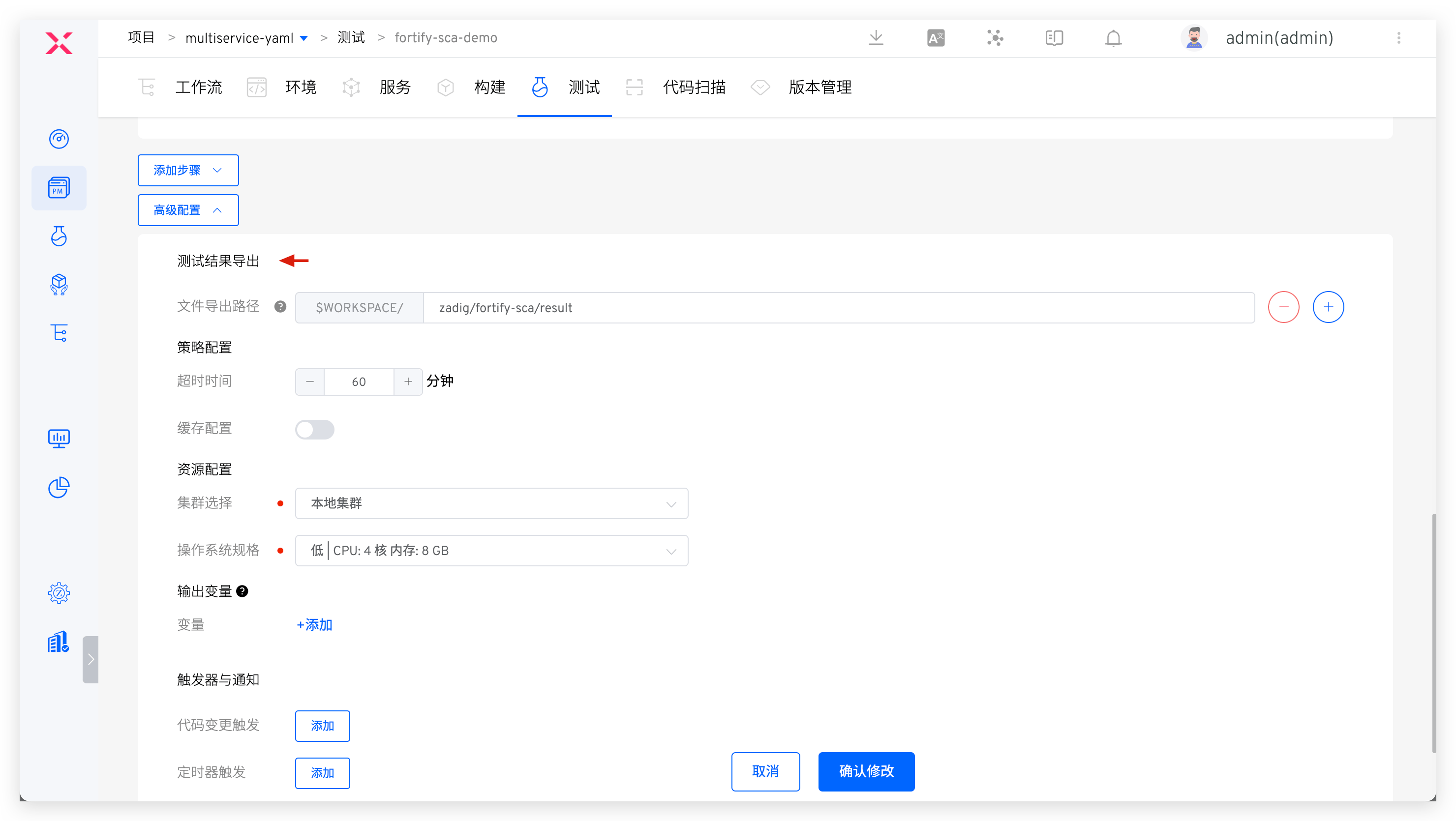
Operating System: Custom image added in Step 1Test Script: Specific command to execute code scan. See Fortify SCA official documentationTest Result Export: Configure path where scan results are located
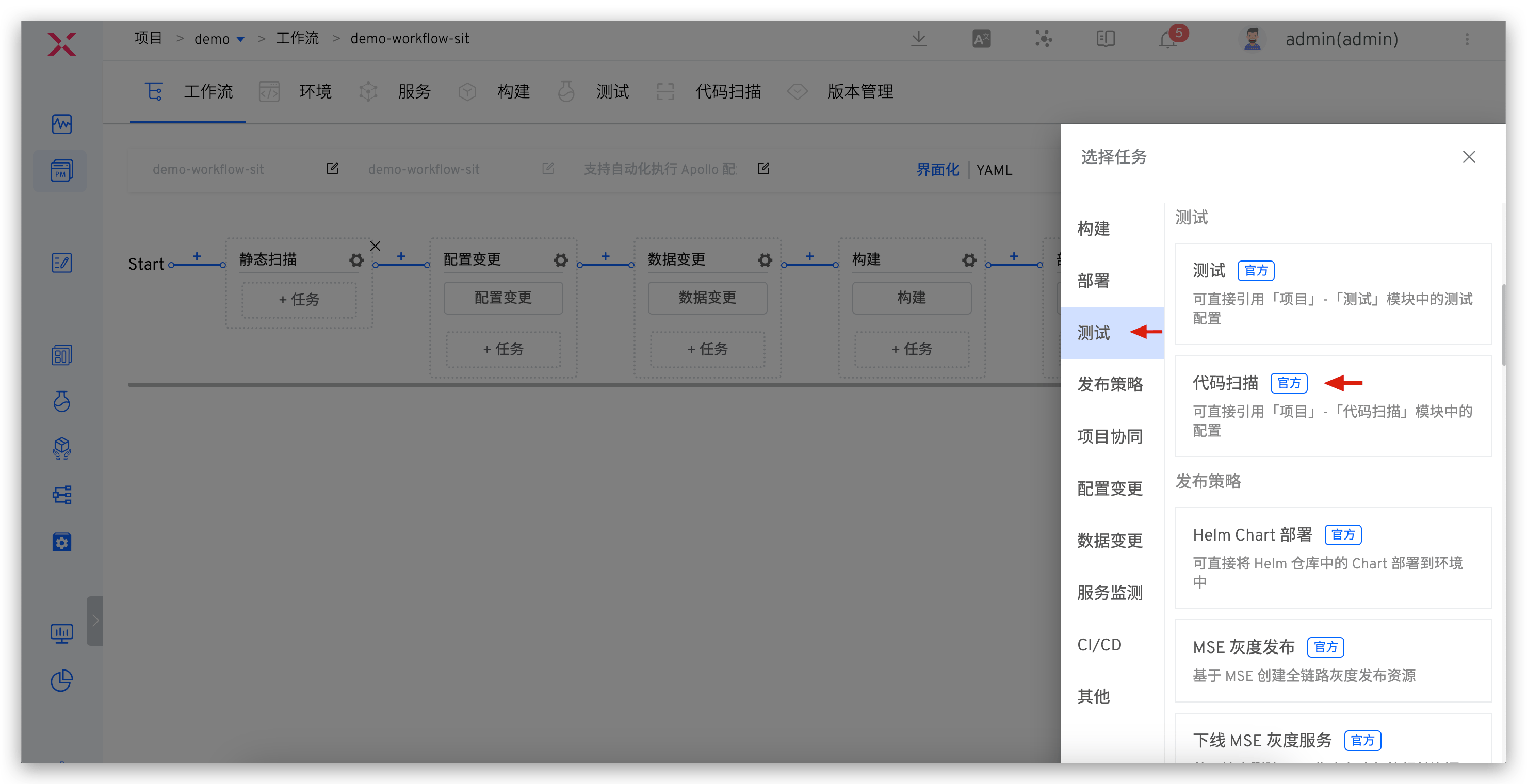
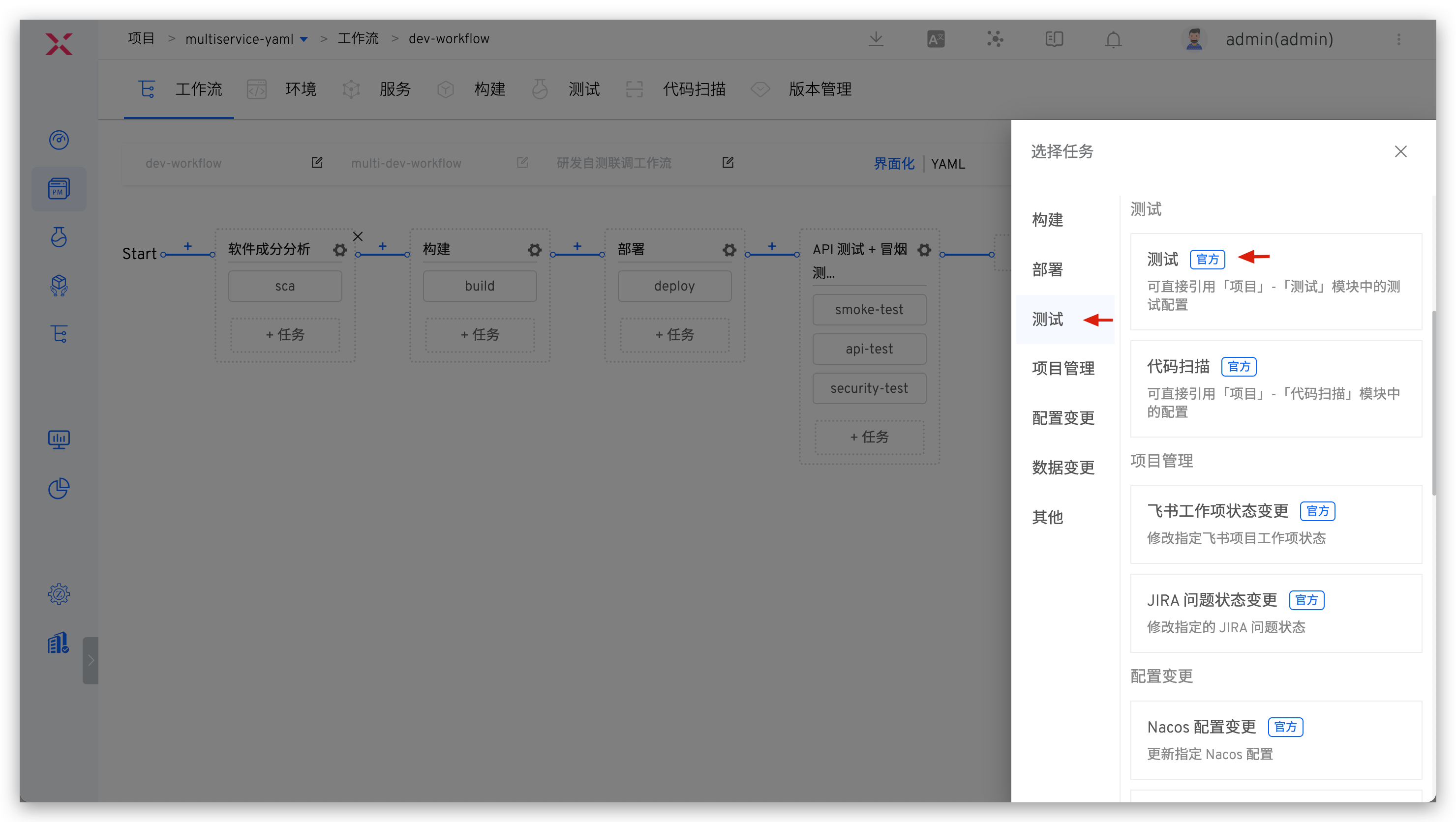
Step 3: Orchestrate SCA Scan
Orchestrate SCA scan in workflow. See: Orchestrate tasks.
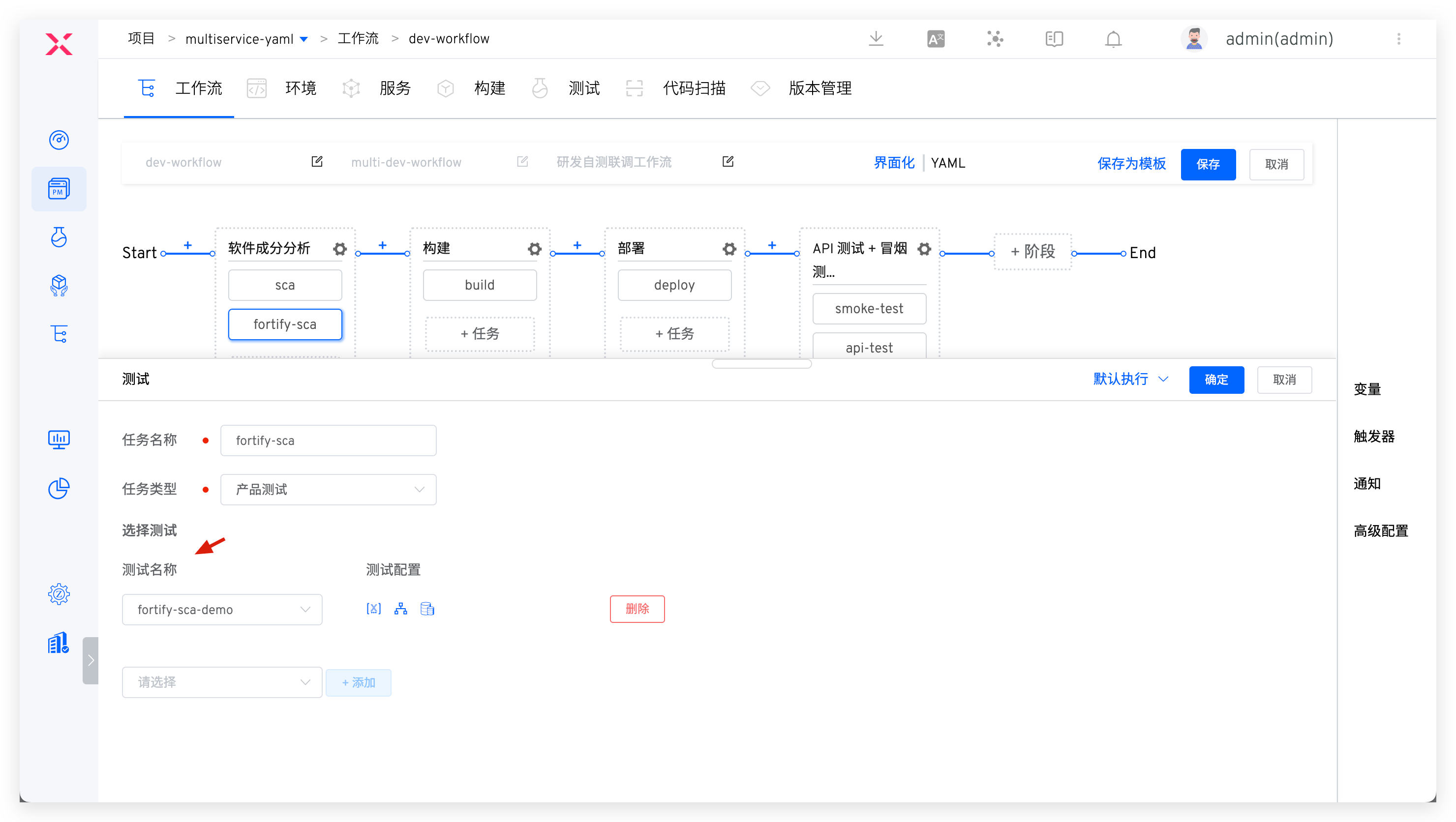
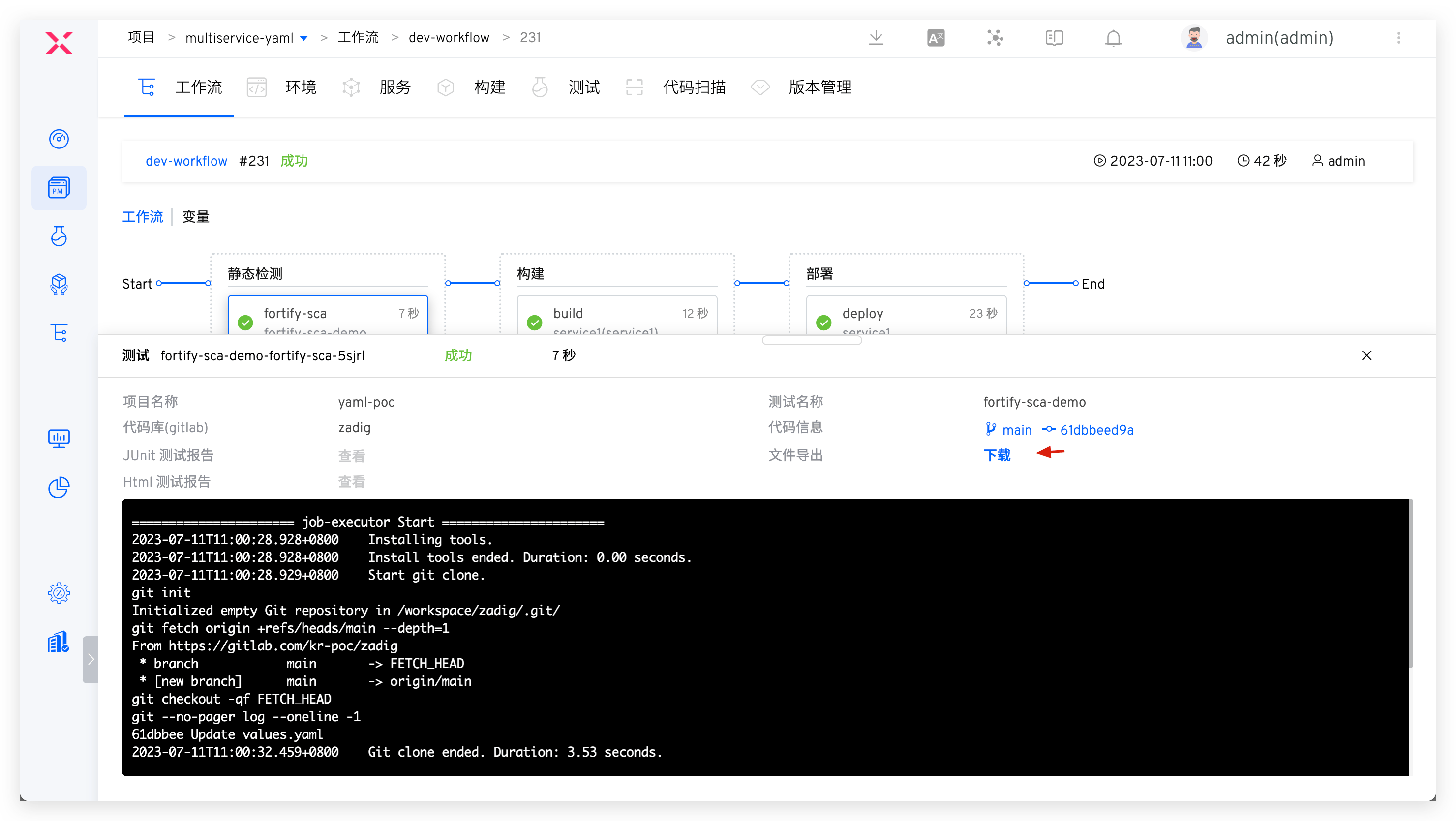
Run workflow. After Fortify SCA execution completes, download scan results for analysis.
# Dynamic Security IAST - DongTai
Step 1: Integrate IAST Capabilities into Service
Modify service YAML configuration, install DongTai IAST Agent, and modify service startup command. Sample service YAML follows:
Tip
Flexibly use Zadig service variable capability in service YAML configuration content, and control whether to install Agent for service on demand. See: Service variables.
// Service Original YAML
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: service1
name: service1
spec:
selector:
matchLabels:
app: service1
template:
metadata:
labels:
app: service1
spec:
containers:
- name: service1
image: dongtai/dongtai-java-agent-demo:0.0.1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
// Service YAML with DongTai IAST Agent
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: service1
name: service1
spec:
selector:
matchLabels:
app: service1
template:
metadata:
labels:
app: service1
spec:
{{- if .iast }}
volumes:
- name: dongtai-iast-agent
emptyDir: {}
initContainers:
- name: agent-init-container
image: curlimages/curl
volumeMounts:
- name: dongtai-iast-agent
mountPath: /tmp
args:
- "-k"
- "-X"
- "GET"
- "The download request URL for the Agent obtained from the DongTai management console"
- "-H"
- "Headers from the Agent Download Request (Retrieved via DongTai Management Console)"
- "-o"
- "/tmp/agent.jar"
{{- end}}
containers:
- name: service1
image: dongtai/dongtai-java-agent-demo:0.0.1
{{- if .iast }}
volumeMounts:
- name: dongtai-iast-agent
mountPath: /agent
env:
- name: JAVA_TOOL_OPTIONS
value: "-javaagent:/agent/agent.jar"
{{- end}}
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
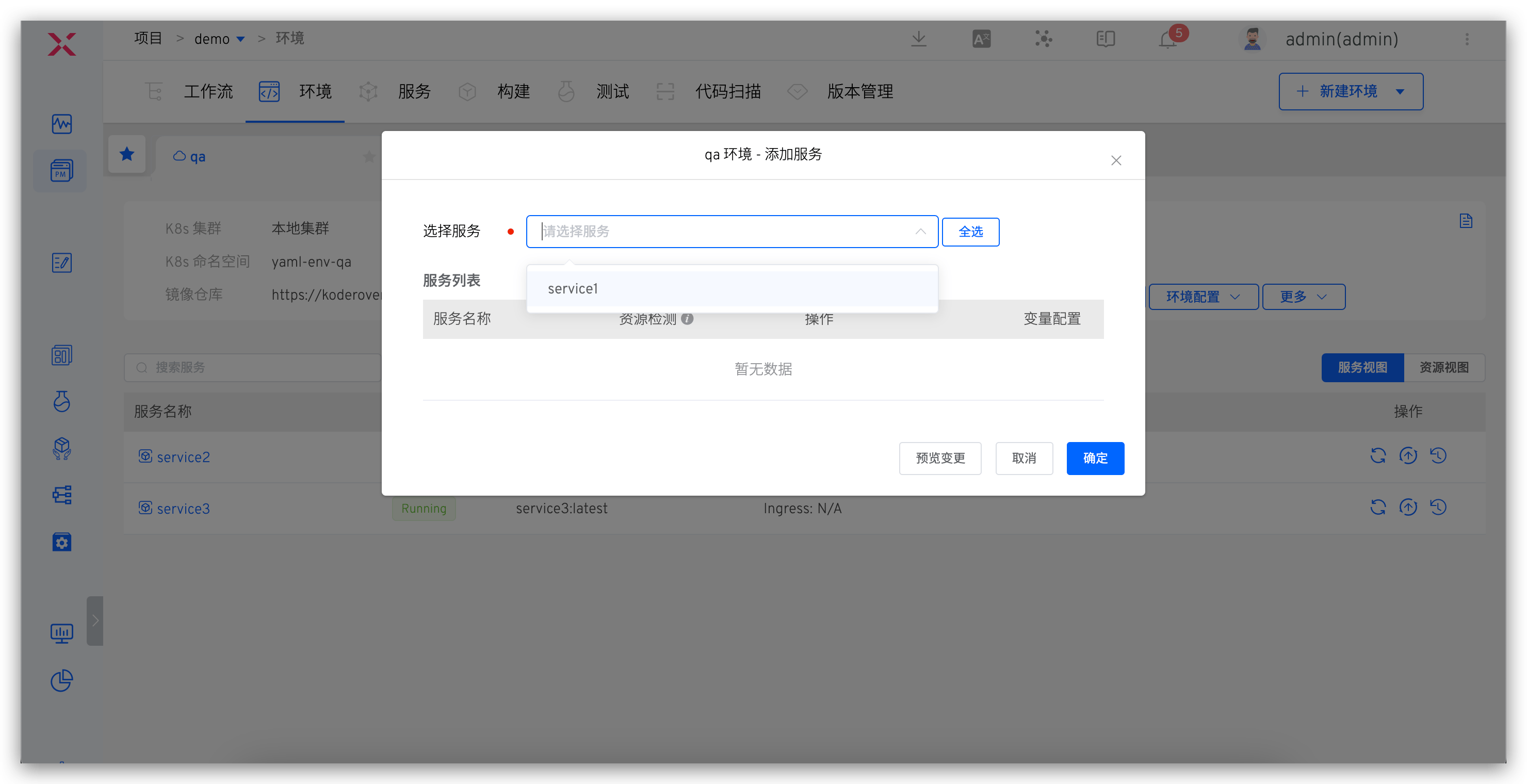
Step 2: Deploy Service to Environment
Deploy the injected IAST Agent service to the environment. See: Add service.
# DevSecOps Core User Scenarios
# Development Stage Static Security Injection
Process: Code Commit > Static Scan > Build > Deploy > Self-test and Joint Debugging
After code implementation and PR submission, static code scanning automatically triggers. Scan results reflect in PR, click to jump to Zadig to view failure reasons, effectively avoiding quality and security risks in code at development source.
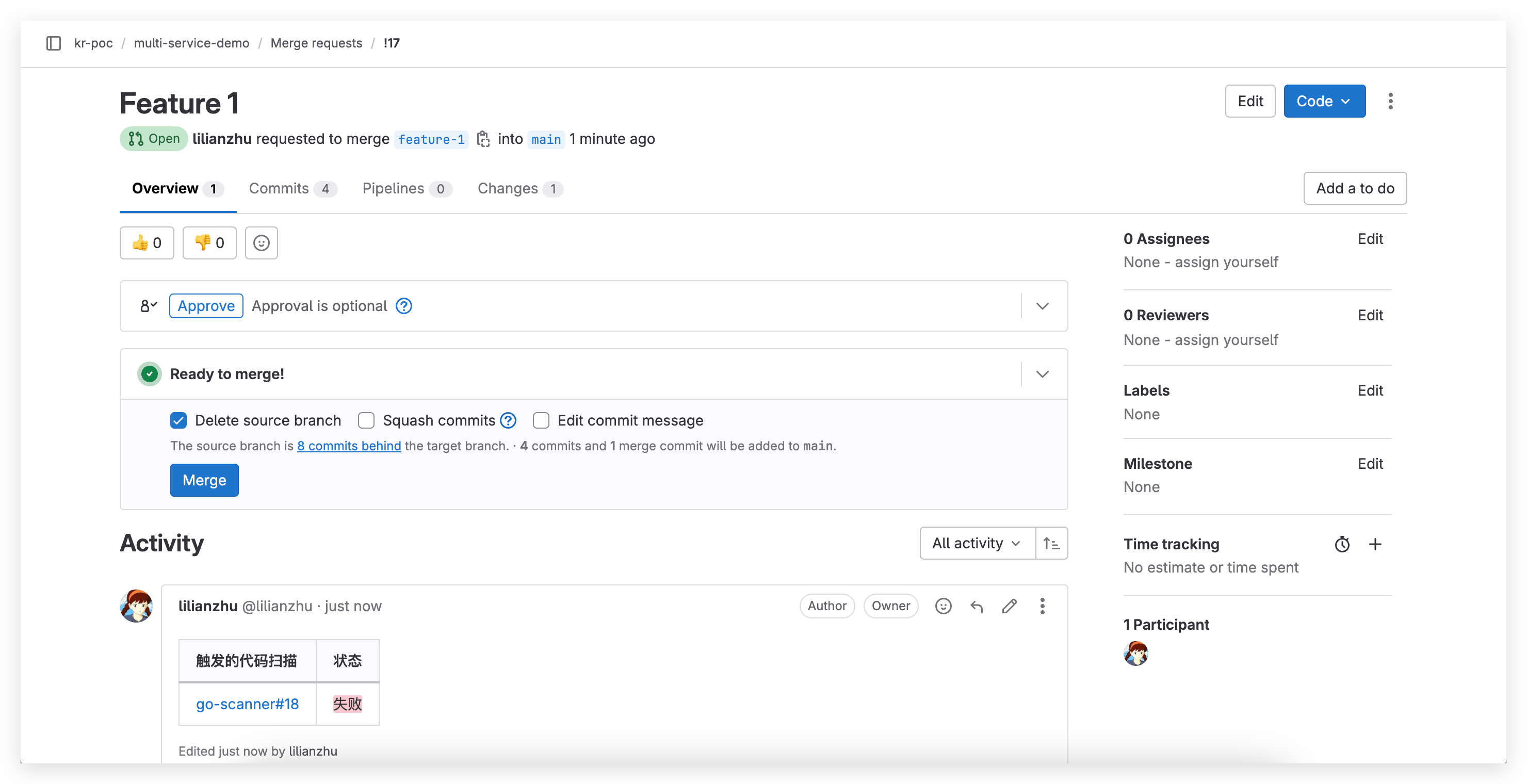
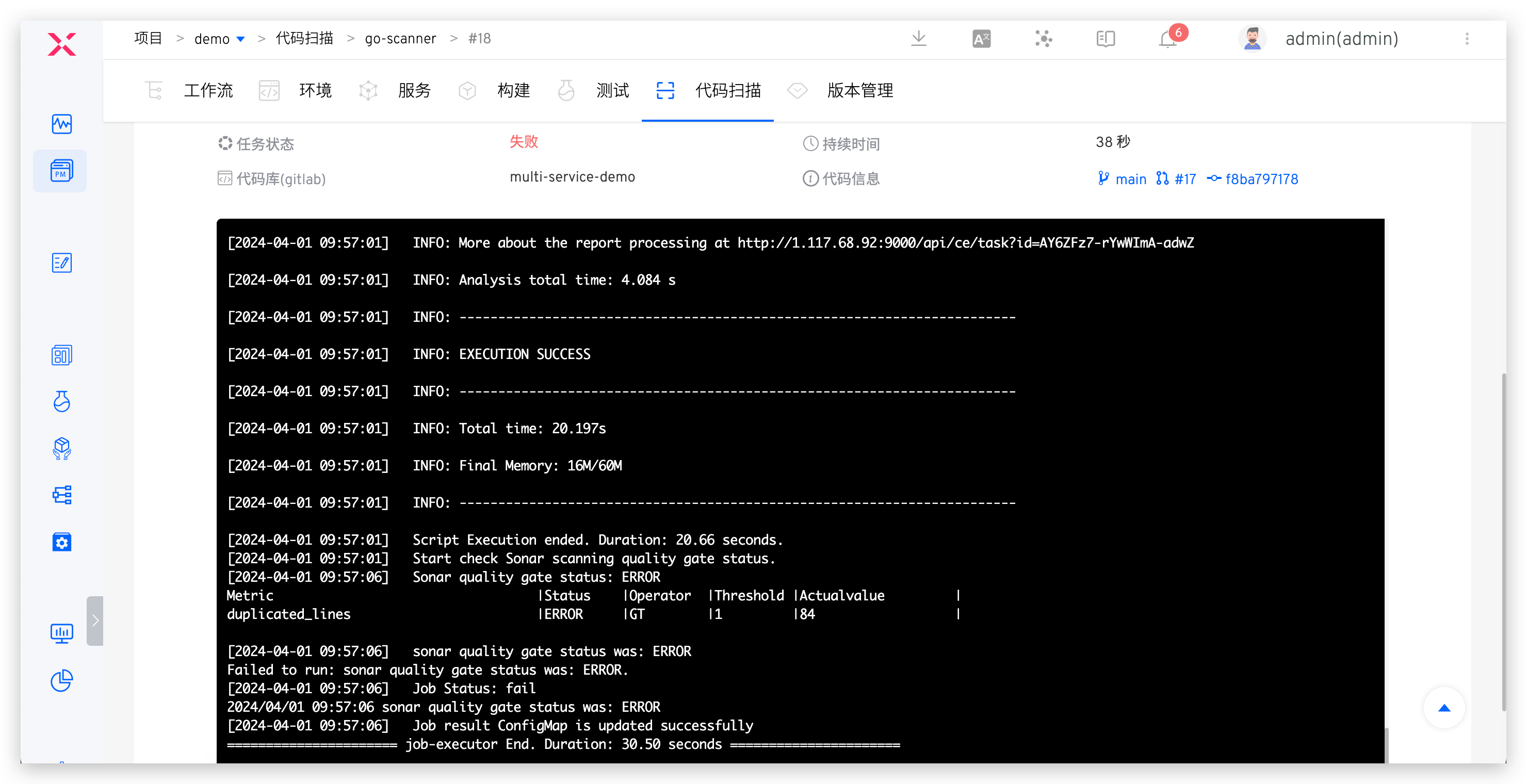
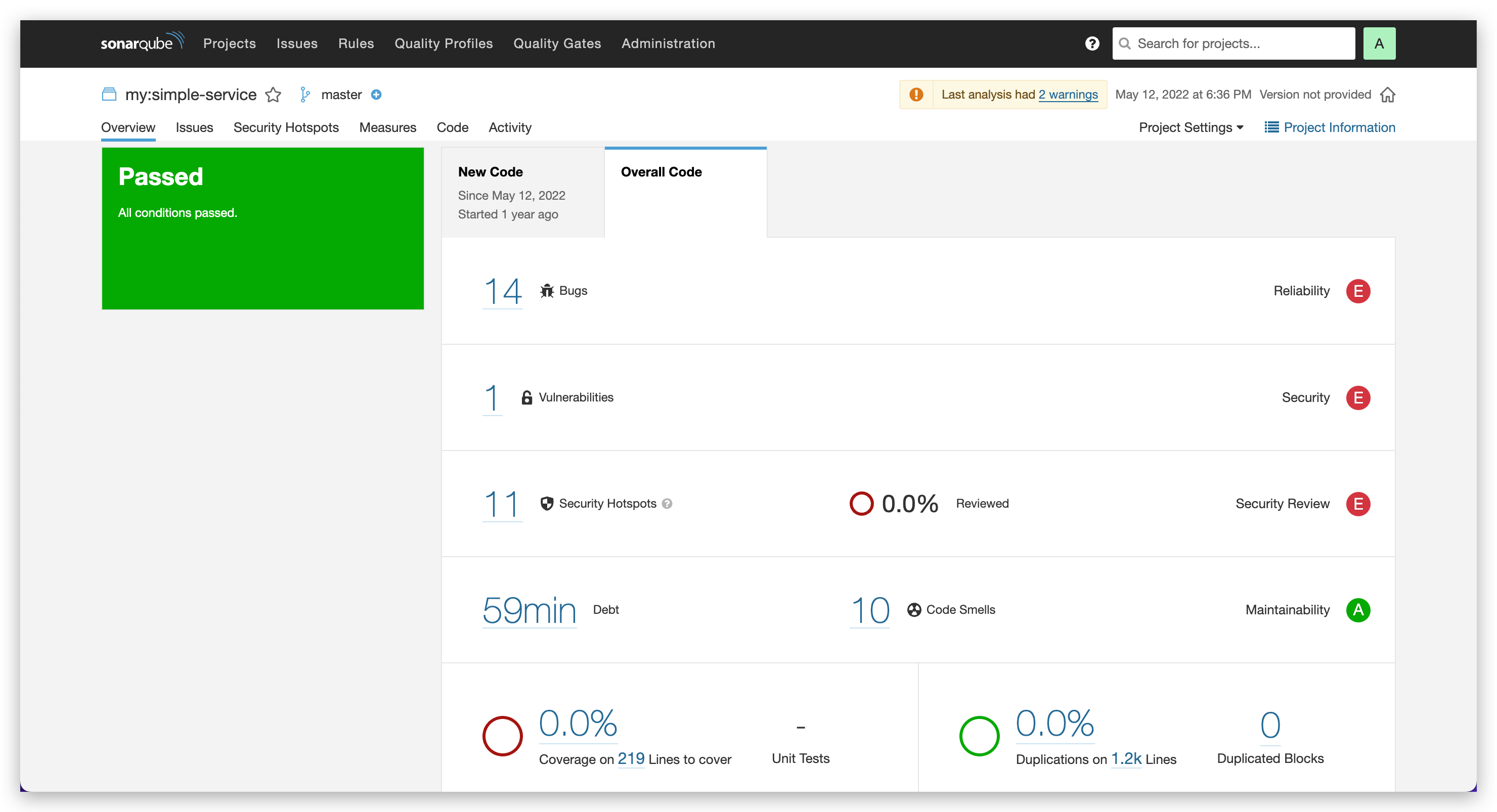
For code scanning using SonarQube tool, click link to jump to Sonar system to analyze more scan results, fix targeted issues, then execute dev workflow for daily self-test and joint debugging.
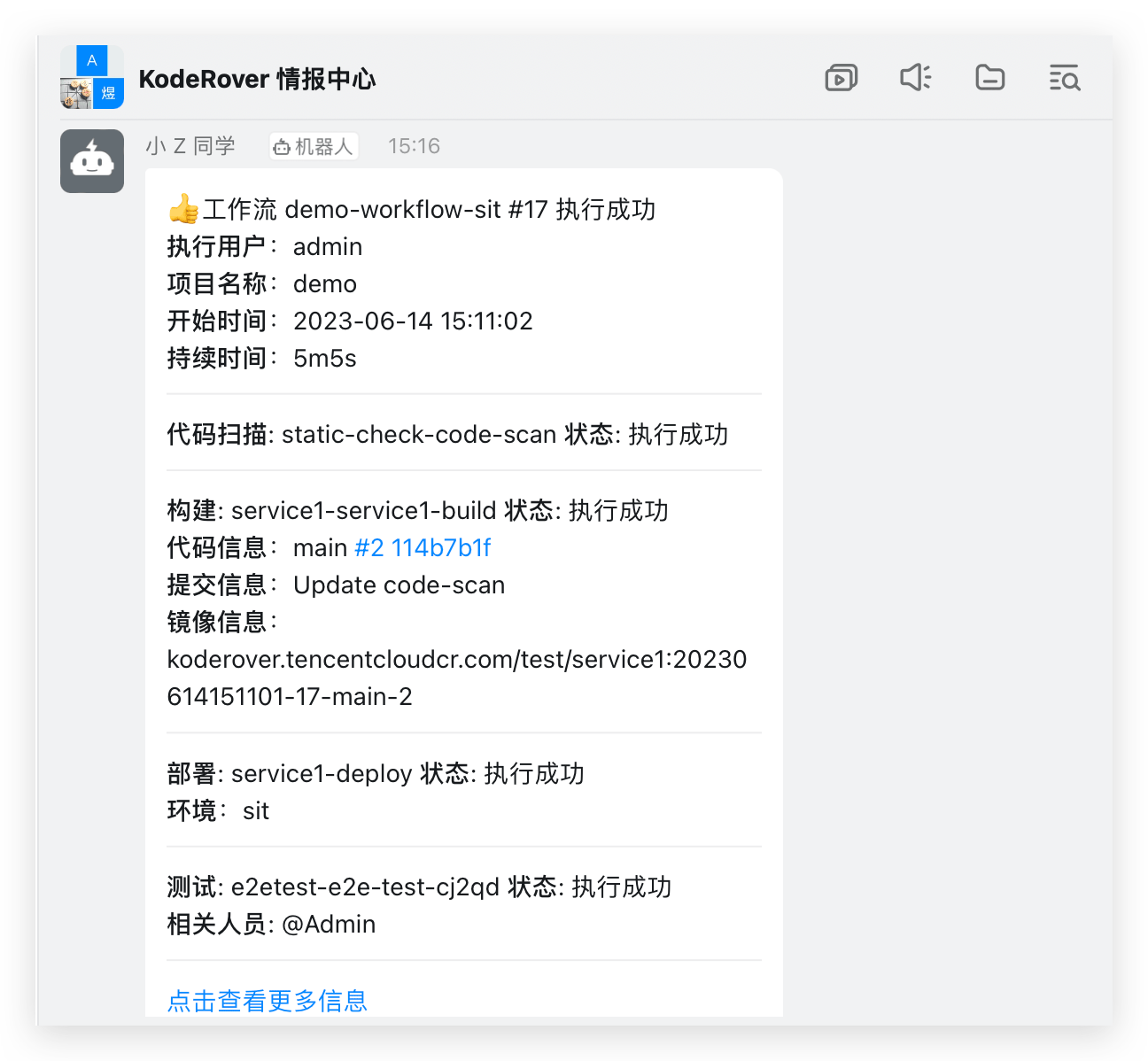
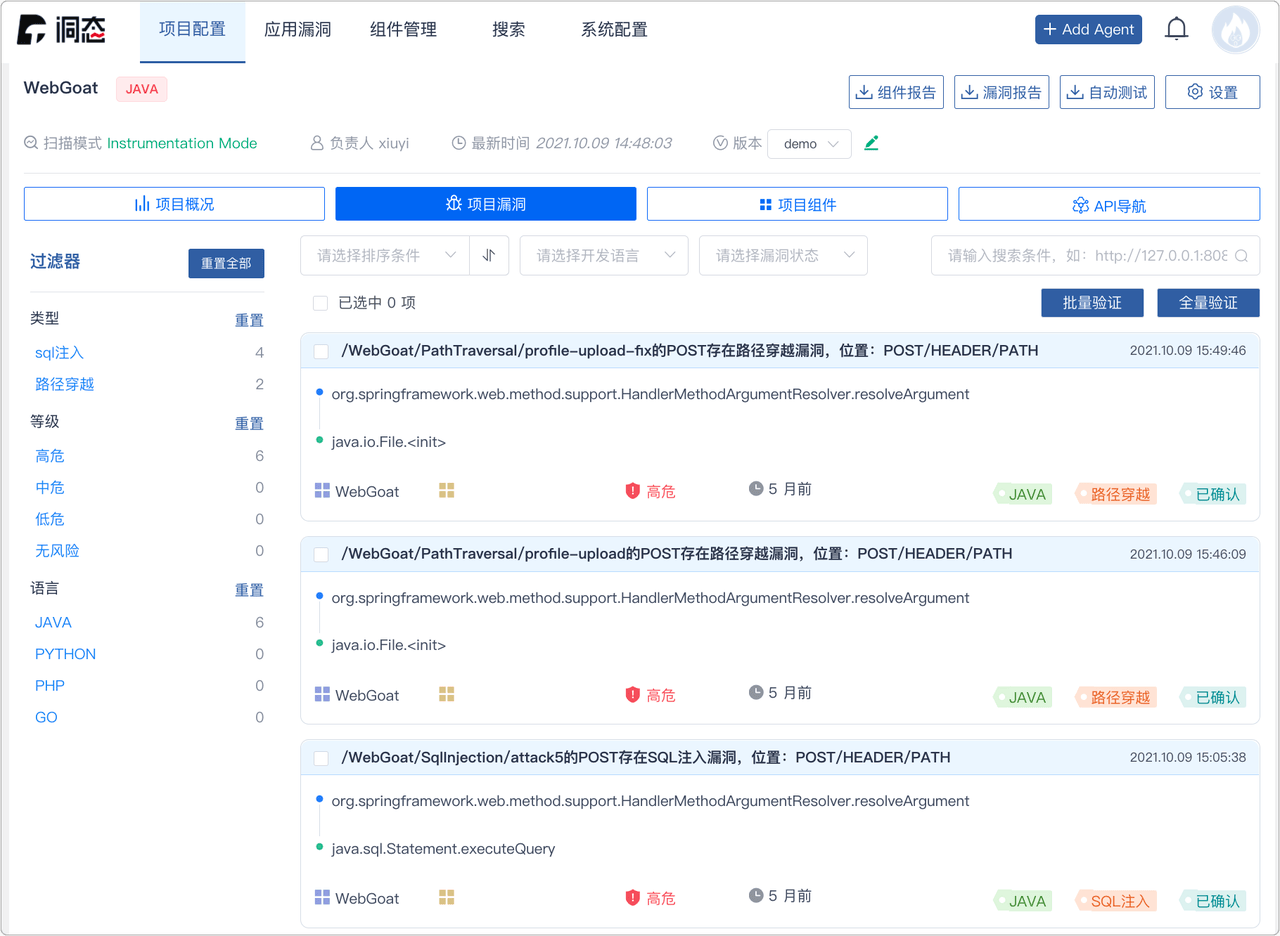
# Testing Stage Combined Security Strategy
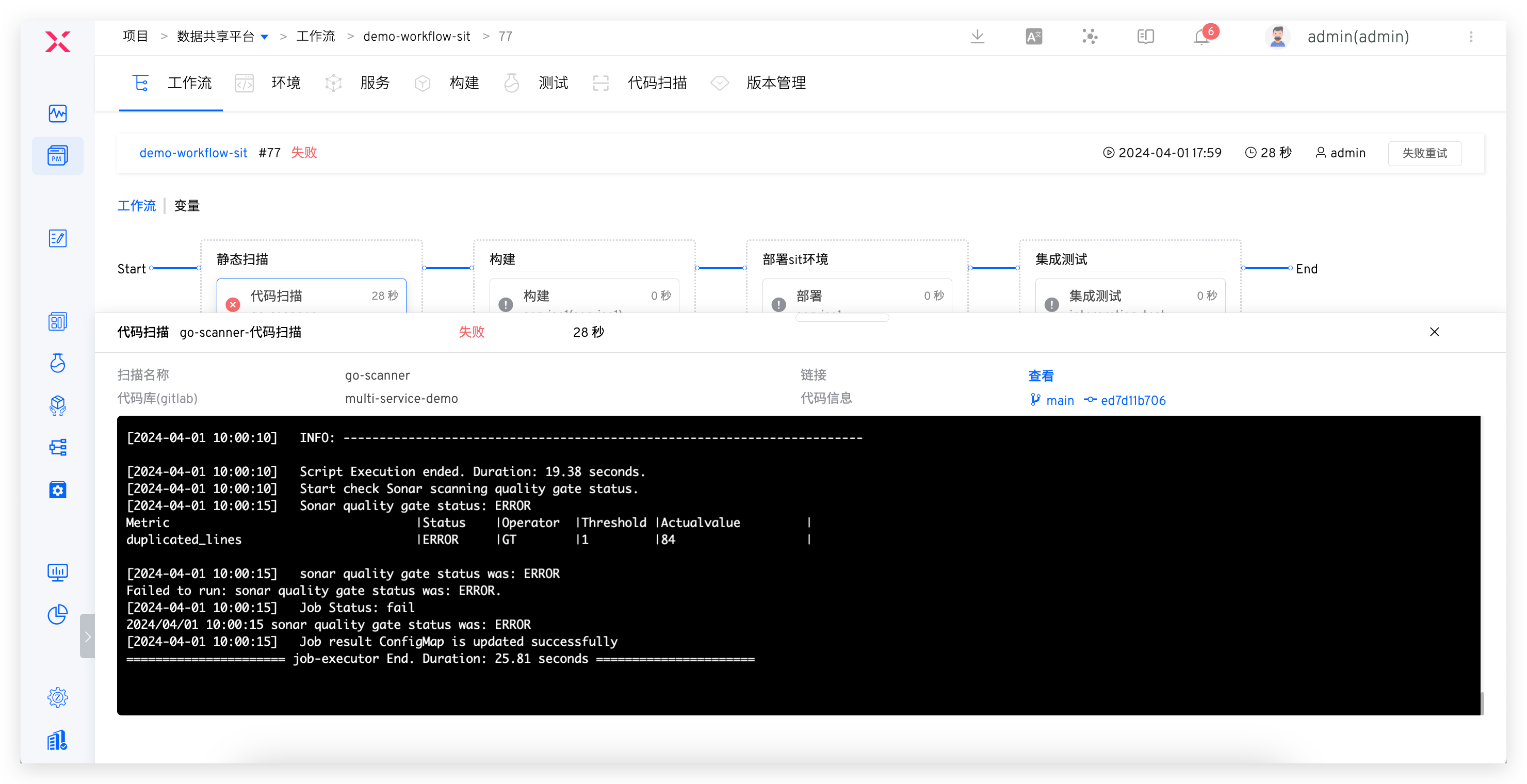
Process: Static Scan (Quality Gate Enabled) > Build > Deploy > Automated Testing (Business Testing + Dynamic Security Detection)
After development testing, test engineer executes workflow based on code branch + PR, deploys integrated test verification environment and performs automated testing. Workflow automatically notifies IM after execution. Login to management console to view dynamic security detection vulnerability details, promote team timely fixes, avoid security risks early.
If static scan task fails, subsequent build and deployment tasks will be blocked. Code changes failing acceptance will be rejected for merge, capturing security risks at source code level and establishing effective quality gate measures. This approach prevents potential issues from entering the system.
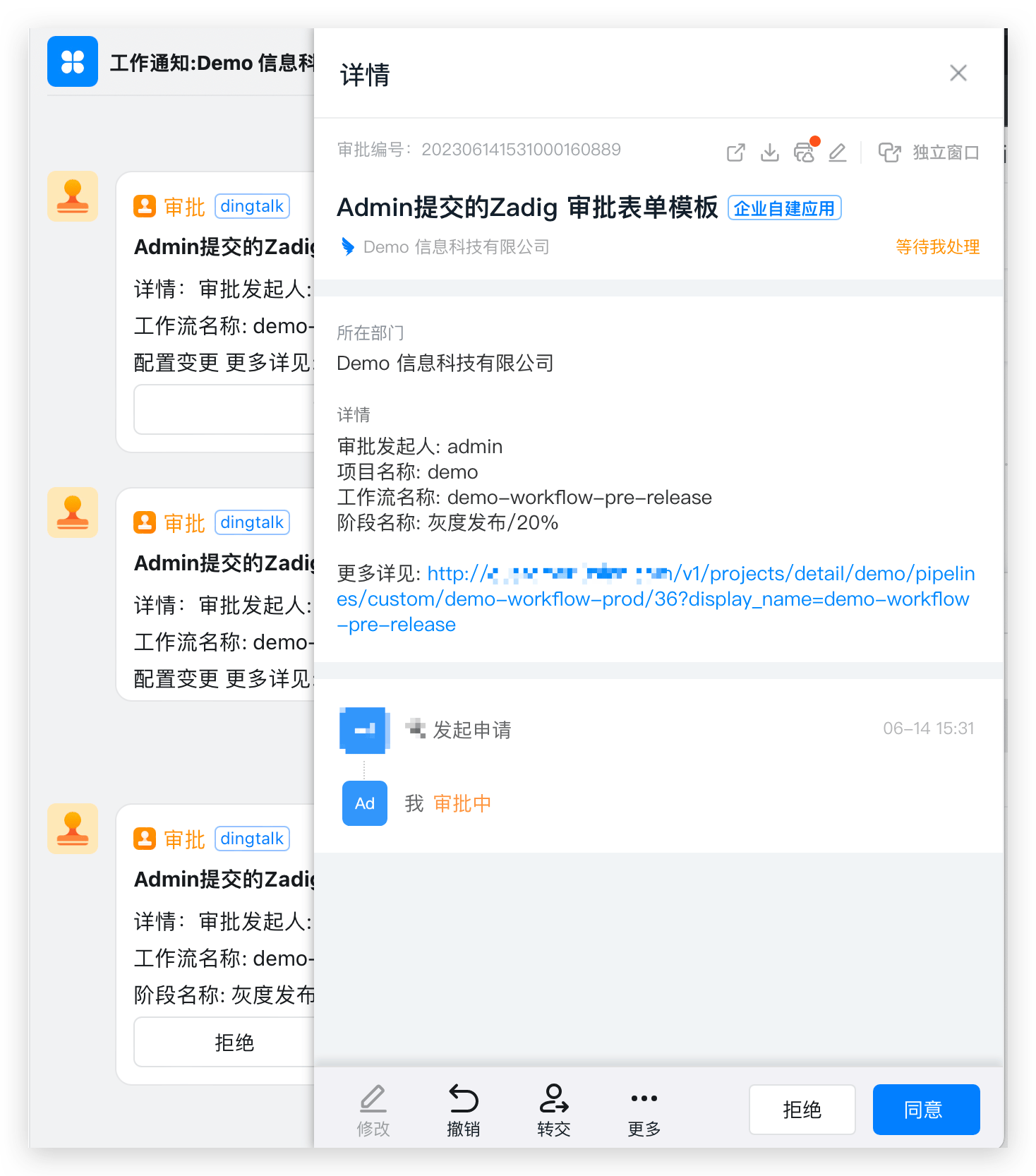
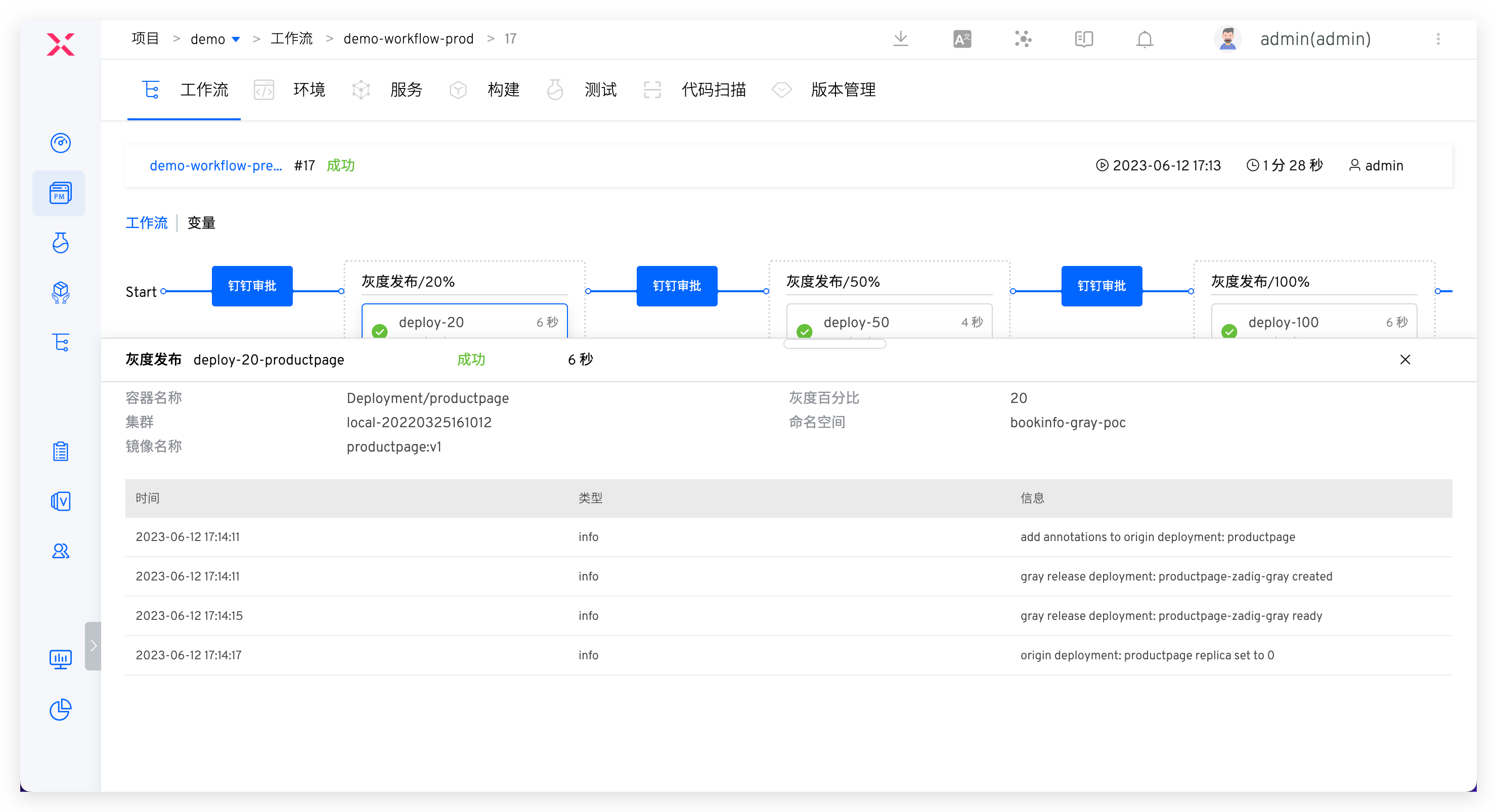
# Release Stage Full Inspection and Approval
Process: Security Committee Review > Batch Gray Release > Automated Testing
After test acceptance, execute prod workflow for production release, approval required before release. Recommended configuration strategies:
- Build release gates, automatically obtain quality results from security scans, unit tests, regression tests, etc., to determine whether release is allowed, serving as checkpoints in release process to ensure version passes acceptance and meets enterprise security requirements before going live.
- Flexibly orchestrate MSE Grayscale, Blue-Green, Canary, Batch Grayscale, Istio and other release strategies to ensure release reliability. See: Release Strategies.
- Add manual approval from security team during release phase to ensure release compliance in business processes.